Configuring Gmail Connector
To include data from Gmail directly in your IPRO
Indexing jobs are run to make data searchable. Indexing must be performed prior to archiving if you intend to search the archived data.
When set up is complete, indexed and archived Gmail content can be viewed, searched, and exported from IPRO Search.
The following configurations are supported:
Gmail + Exchange (on-premise AD)
Gmail + O365 Azure AD
Gmail + AD (no email backend required)
Successful configuration of the Gmail Connector involves the following steps:
- Set up Google Cloud Configuration
- Create a new Google Cloud Project to run the Gmail Crawler Service Account
- Configure Impersonation using OAuth 2.0 for Server to Server Applications
- Create a Service Account
- Enable API access for the Admin API and the Gmail API
- Delegate domain-wide authority to the Service Account
- Configure the Gmail Connector in the IPRO Admin UI.
When the Gmail Connector is configured, make sure to map all users and set up the required Indexing and Archiving jobs.
First, create a new Google Cloud project. The Google Cloud project provides context for the Service Account that is used by the crawler application to impersonate access to user mailboxes. To create the Google Cloud Project required to run the Gmail Crawler Service Account, see steps below.
- Open the Google Cloud Platform Console. Log in using G Suite Admin credentials.
- From the Google Cloud Platform home page, navigate to IAM & Admin > Manage Resources.
-
Then, click Create Project.
- Give the new Google Cloud project an appropriate name, and select the correct (parent) organization.

-
TIP
For more information on how to create and configure a Google Cloud Project—see Creating and managing projects.
First, create the Service Account. Then, enable API access for the Admin API and the Gmail API. Lastly, delegate domain-wide authority to the Service Account.
Creating the Service Account
Service Account credentials include an auto-generated, unique email address and at least one public/private key pair. If domain-wide delegation is enabled, the Service Account credentials also contain a Client ID.
To obtain the credentials in the Google Cloud Platform Console, see steps below.
- First, generate the Service Account credentials.
- From the Google Cloud Platform home page, navigate to IAM & Admin > Service Accounts.

- From the Service Accounts dashboard, select the Google Cloud Project previously created.
- To create a new Service Account, select Create Service Account.

- Do the following in each corresponding field:
- Enter an appropriate Service account name.
- Enter the Service account ID.
- (Optional) Enter an appropriate Service account description.
- Click Create, click Done.
- Next, generate the public/private key pair. Select the previously created Service Account email address from the email addresses listed.
- Navigate to the Keys tab. Expand the Add Key dropdown menu and select Create new key.
- Download the file that contains the private key. Opt for the JSON Key type. Create and download the private key locally.

-
IMPORTANT
Store the private key in a secure location. If lost, the key cannot be recovered.
Enable API access for the Admin API and the Gmail API
Perform the following steps in the Google Cloud Platform Console.
-
From the Google Cloud Platform home page, navigate to APIs and Services > Enabled APIs & services.
-
From the Enabled API & services dashboard, click Enable APIs and Services.
-
Add and enable the Admin API and the Gmail API.
TIP
Use the search bar function to find the Admin API and Gmail API. 

Delegate domain-wide authority to the Service Account
To delegate authority to the Service Account, use the value copied as the Client ID.
-
To grant G Suite domain-wide authority to the Service Account, navigate to the Service Accounts section. From the Google Cloud Platform home page, go to IAM & Admin > Service Accounts.
-
Select the previously created Service Account email address from the email addresses listed.
-
Copy the value populated in the Unique ID box.
-
The Unique ID value is used as the Client ID required to delegate authority to the Service Account.
-
From the G Suite Domain Admin Console, navigate to Main menu > Security > API Controls.
-
In the Domain-wide Delegation pane, select Manage Domain Wide Delegation.
-
Click Add new.
-
In the Client ID field, enter the Service Account's Client ID (Unique ID).
-
In the OAuth scopes (comma-delimited) field, enter the following list of scopes :
-
https://www.googleapis.com/auth/admin.directory.user.readonly,https://www.googleapis.com/auth/admin.directory.group.readonly, -
https://www.googleapis.com/auth/gmail.readonly, -
https://www.googleapis.com/auth/gmail.settings.basic, -
https://www.googleapis.com/auth/gmail.labels. -
Click Authorize.
You have now granted the application the authority to make API calls impersonating the users in your domain.
For additional details on how to create a Service Account and delegate domain-wide authority—see Creating and managing service accounts and Using OAuth 2.0 for server to server applications.
Perform the following steps in the IPRO Admin UI. Administrator rights are required.
- Log into the IPRO Admin UI.
- Select Archiving.
- Open the Connectors tab.

- Navigate to the Locations section. Click Add.
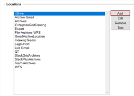
- Expand the Live Locations drop-down menu. Select Email (Gmail).

- Click Next.
- The Gmail Store configuration window displays.

- In the Name field, enter a relevant name for the live location.
-
TIP
Choose a location name that is meaningful to the users and reviewers who will be accessing the archive data. The name is also used by the indexing service. To change the location name, a new location must be created and its data reindexed. - Enter the User ID you wish to index.
- Enter the Domain(s) you wish to index.
- Add the relevant Key File.
- (Optional) Distribute accounts across all crawler nodes. This is checked by default for a better balancing of the indexing workload.
- (Optional) User Group. This represents the users whose Teams content will be indexed and made available in an IPRO Search.
- (Optional) Click Test to verify the Audit Path connection.
- Click Save.
- At the bottom of the Connectors tab, click Save.
Following connector and location configuration, perform User Mapping. For more information—see User Mapping. For detailed steps—see Configuring User Mapping
Next, configure Indexing and Archiving jobs to process the Gmail source data—see Configuring Gmail Indexing and Configuring Gmail Archiving.






