Phishing
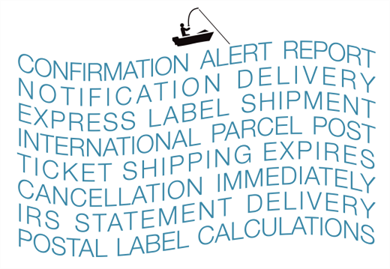
Phishing attacks, or attempts to trick email users into giving out personal information, have become both commonplace and sophisticated. Many organizations are ill-equipped to deal with phishing attacks, stemming from deficiencies in several areas. There could be a lack of education and training about how to spot a phishing attack and react to it effectively. The organization may be trained but lacking the tools to respond appropriately.
The most common scenario is that the security manager has implemented the necessary training and configured an email security solution to intercept suspected phishing attacks. The security manager has done everything right, but despite these efforts, phishing attacks still occasionally flow into the mail system. Why?
The nature of a phishing attack is to be deceptive, to resemble a harmless message and often to mimic the style and language of a known and whitelisted sender. Because of this, the security manager cannot set alerts for all possible phishing attacks, because you never know what form the attack will take.
Despite this, REMEDIATE is an excellent tool for removing identified phishing messages that have entered the mail system. A typical workflow is that an employees receives a suspicious message and notifies the security manager, who immediately runs a case to find all recipients of the message and quarantines every item found.
A phishing attack is a great opportunity to retrain staff on how to react and who to inform if they receive a suspicious message.